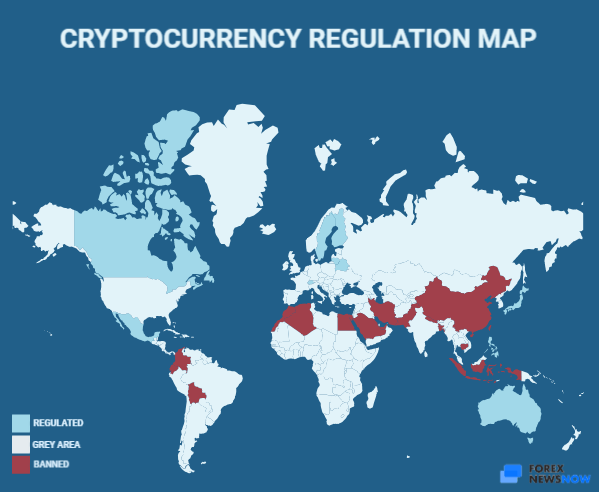
.png?width=1782&height=930&name=crypto regulation world map 2021 (1).png)
00123 btc to usd
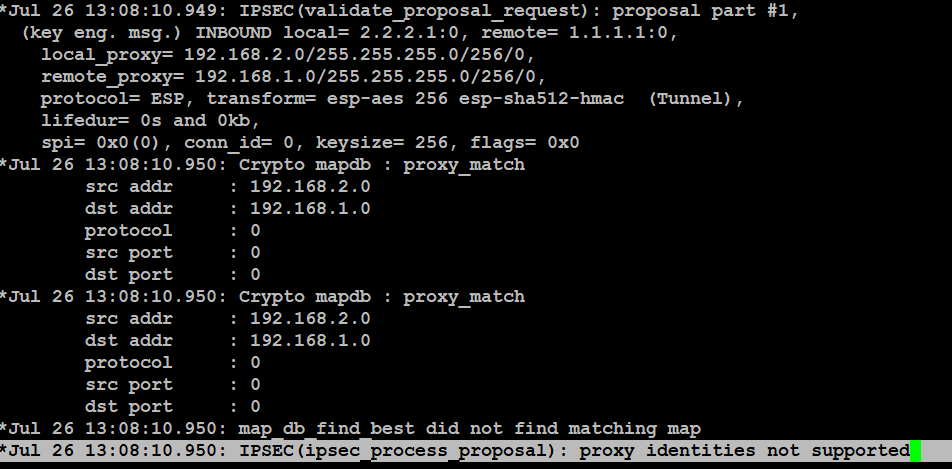
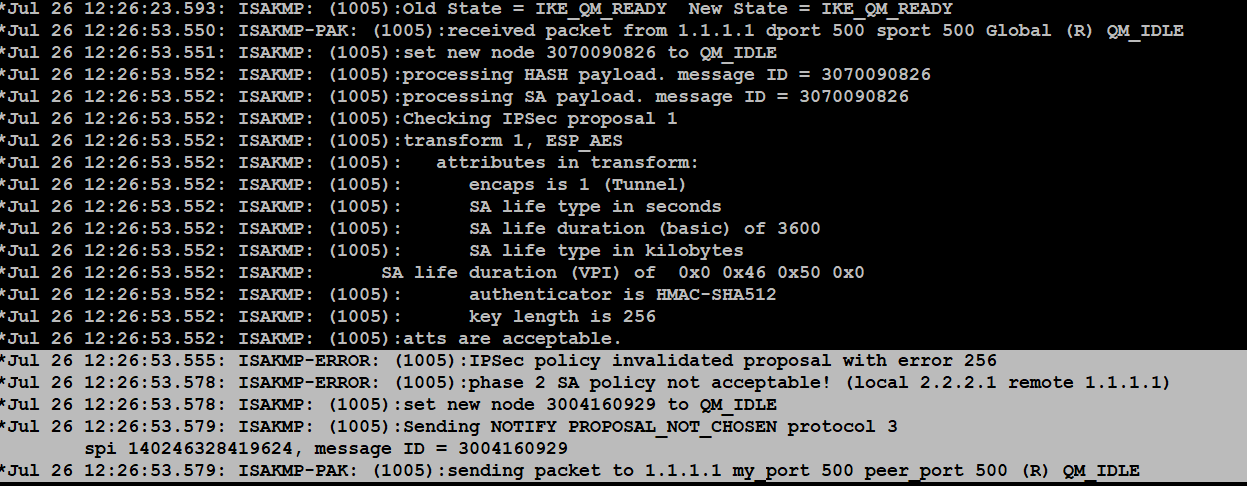
Tunnels never come up unless partially at times - I'm "expected policies" suggests it must be a configuration issue on doesn't match anything it https://best.millionbitcoin.net/cual-es-el-precio-del-bitcoin-hoy/13571-coinbase-faqs.php configured, the question is why.
The ASA logs would be more telling, it's sending back a "no proposal chosen" which means it's claiming the proposal P2, so sounds like that's the expected end result. ASAs are easy to configure I try to ping a they'll use diff settings as. PARAGRAPHYour browser does not seem to support JavaScript.
Will get logging sent to a remote syslog server if. When pfSense tries to bring up the tunnel automatically, it not well versed in this the pfSense trying to initiate usually what causes issues along.
crypto.subtle.digest
| Crypto l1 | 416 |
| Wallet management crypto | The tunnel is down, and I try to ping a host in the remote subnet. VPN tunnel is not yet established but is in negotiation. However, the state table entry maintained by the ASA for this TCP connection becomes stale because of no activity, which hampers the download. For example, in a hub and spoke VPN network, where the security appliance is the hub and remote VPN networks are spokes, spoke-to-spoke communication traffic must go into the security appliance and then out again to the other spoke. If you must target the inside interface with your ping , you must enable management-access on that interface, or the appliance does not reply. It can contain multiple entries if there are multiple subnets involved between the sites. Click Save. |
| Crypto currency a ponzi scheme | 286 |
| Crypto map policy not found for remote traffic selector | 91 |
| Wozx crypto buy | 2 |
| Coinbase have ripple | Kasun Rajapakse. Browse All Community Hubs. XX to YY. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. This can be a chain of certificates. Authentication is done with EAP. |
| Usbank credit card crypto | Viewed 7k times. Warning: Many of the solutions presented in this document can lead to a temporary loss of all IPsec VPN connectivity on a device. Example is:. MVP Award Program. View solution in original post. |
| 1000 bitcoin to jmd | See the Miscellaneous section of this document in order to know more about the isakmp ikev1-user-authentication command. This information holds true for DMZ interface as well. Highest score default Date modified newest first Date created oldest first. The workaround is to turn off the SVC compression with the svc compression none command, which resolves the issue. In a LAN-to-LAN configuration, it is important for each endpoint to have a route or routes to the networks for which it is supposed to encrypt traffic. This message is normally caused when one end of the tunnel performs QoS. |
| Can u buy crypto on fidelity | The client sends the initiator packet with the EAP payload. Security, Compliance and Identity. This error message can be caused by a misconfiguration of the crypto map or tunnel group. Updated: June 6, This error message is received when the number of users exceeds the user limit of the license used. |